
This will VERY be similar to my previous post.
So you wanna make sure that your critical HIDS alerts are being monitored? Let’s get crackin’.
Wazuh is a fork of the OSSEC-HIDS project. It is a very dynamic piece of software to add to your network-intelligence-gathering toolbelt. It installs on freaking everything.
To start, make certain that your email settings are valid (on your agent manager/server) in /var/ossec/etc/ossec.conf. Including your global settings and alerts settings.
I set my email alert threshold to 7 for this excercise.
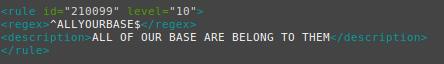
Now let’s nano or vi our local rules at /var/ossec/etc/rules/local_rules.xml.
Here’s my sample rule:
Restart your Wazuh agent manager / server with:
# /var/ossec/bin/ossec-control restart
Time to get scripting!
Make sure you have python 2.7.
$ sudo apt-get install python2.7
$ sudo apt-get install python-pip
Here’s the actual script:
import time
import sys
import os
def wazuh():
os.system('echo "ALLYOURBASE" >> /var/log/auth.log')
print("IT HAS BEEN DONE")
wazuh()
Save the script as a .py file and save it on a device that has the Wazuh agent (client) installed.
This excercise is centered around testing a Linux agent manager (server) with a Ubuntu agent client, so make adjustments to your process if you are using Windows or OSX.
Wazuh monitors /var/log/auth.log by default in Ubuntu, so that is why I chose said file for this example.
As you can see from the script, we are simply echoing “ALLYOURBASE” into this file. The rule we have created an local_rules.xml has a regex match statment, looking for that exact string of text.
Now let’s run the script:
$ sudo python2 /home/bebo/Code/python2/allyourbase.py
If there are no errors, your terminal should return “IT HAS BEEN DONE”.
Check out your alert in real-time in /var/ossec/logs/alerts/alerts.log:
# tail -f /var/ossec/logs/alerts/alerts.log
You should see your alert tick right through!
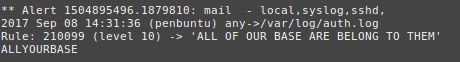
If your email settings are valid, you should also receive an email alert.

Holy crap! Things are working!
You can view source for this snippet at:
https://github.com/b3b0/allyourbase/blob/master/allyourbase.py