
There are times that we need to make sure that we have granular control over how well our IDS is alerting. Sometimes you may as well put yourself into a tizzy asking, “Am I able to see what I REALLY need to?”
A way to accomplish this with Security Onion is to create custom rules in /etc/nsm/rules/local.rules
My rule will be simple.
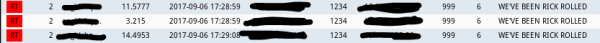
alert tcp any any -> $HOME_NET 999 (msg:"WE'VE BEEN RICK ROLLED"; content:"NEVERGONNAGIVEYOUUP"; flow:to_server; classtype:diagnostic; sid:12000006; rev:1)
If you have already defined your home network, then this is pretty straight forward. I used a sid that I was certain not to fire another rule message name.
In /etc/nsm/securityonion/sguild.email, configure your sguild alerts to alert on this sid:
# EMAIL_ENABLE_SIDS: A list of snort IDS (sids) that you want to enable, but are NOT
# included in EMAIL_CLASSES. NOTE: This overrides EMAIL_DISABLE_SIDS.
# 0=none
set EMAIL_ENABLE_SIDS "12000006"
Perform:
# nsm_server_ps-restart && rule-update
Now your Security Onion box is ready to alert you.
Let’s make a script now!
Make sure you have python 2.7 and python-pip:
$ sudo apt-get install python2.7
$ sudo apt-get install python-pip
Then let’s get the scapy library for Python:
$ sudo pip install scapy
The actual script is very simple:
import time
import sys
import os
from scapy.all import *
list = open("dests.txt").readlines()
#####################
#if you want to specify many destinations to test multiple sensors, use this list statement.
#####################
def ids():
for x in list:
packet = IP(dst=x,src="YOUR IP")/TCP(dport=999,sport=1234)/"NEVERGONNAGIVEYOUUP"
send(packet)
print("A PACKET HAS BEEN SENT TO " + x)
time.sleep(2)
ids()
Make sure to put in a source IP that is routable on the network from the location in which you launch this script.
Finally, save this script as a .py file and run it. Like so:
$ sudo python2 /home/bebo/Code/python2/rickroll.py
If you don’t get any error messages, then you can check SGUIL and your email for alerts.
Success!
You can view source for this snippet at:
One thought on “Security Onion: Testing your rules with Python 2.7 & the SCAPY library”